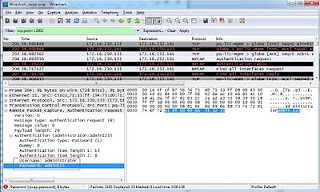
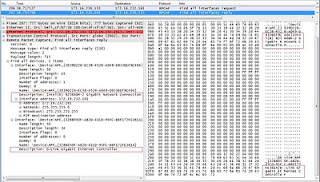
Below snapshot shows HTTP request which Bittorrent Client uses to communicate with Bittorrent Servers. In the request we can see different parameters like client id, port number.
We can observe that Bittorrent client uses different User Agent request headers like BTWebClient, Bittorrent etc.
UDP is using Source port as 24615, which is being communicated to Bittorrent Server as HTTP Request.
So we can detect or block Bittorrent based on HTTP Request URI or User-Agent header strings or UDP protocol communication.
Below are few Signatures which we can use to detect Bittorrent.
alert udp any any -> any any ( msg: "Bit Torrent UDP"; content:"41 02"; offset:0; depth:2; content:"38"; offset:13;depth:1; content:"08"; offset:21;depth:1; sid:8888881; rev: 1; )
alert udp any any -> any any ( msg: "Bit Torrent Protocol"; content:"|13|bittorrent|20|protocol"; offset:0; sid:8888882; rev: 1; )
alert udp any any -> any any ( msg: "Bit Torrent UDP Communication"; content:"d1|3a|ad2|3a|id20|3a|"; sid:8888883; rev: 1; )
Below Signature triggers and alerts when the content is seen in HTTP Request URI
alert tcp any any -> any 80 ( msg: "Bit Torrent: HTTP Request"; content:"info_hash="; pcre:"/announce\?info_hash=/Ui"; sid:8888884; rev: 1; )
Observed following User-Agent strings as part of HTTP Requests
User-Agent: BitTorrent/7610(27328)
User-Agent: BTWebClient/7610(27328)
which can be detected using following Signatures
alert tcp any any -> any 80 ( msg: "Bit Torrent: HTTP User Agent 1"; content:"User-Agent: BitTorrent"; sid:8888885; rev: 1; )
alert tcp any any -> any 80 ( msg: "Bit Torrent: HTTP User Agent 2"; content:"User-Agent: BTWebClient"; sid:8888886; rev: 1; )
Posts related to Snort IDS/IPS which might be of interest to you.
http://darshanams.blogspot.in/2011/05/snort-logging-alerts-to-syslog-server.html
http://darshanams.blogspot.in/2010/06/snort-preprocessors-and-alerts.html
http://darshanams.blogspot.in/2012/05/installing-snort-from-source-as-ips.html
To know about Google Talk Jabber protocol communication
http://darshanams.blogspot.in/2008/11/deciphering-google-talk-jabber.html
For Zebra/Bittorrent protocol communication
http://darshanams.blogspot.in/2009/03/i-was-just-checking-my-mails.html
P.S Signatures given above are neither tested nor fine tuned. Just an
idea how to detect Bit Torrent communication.
idea how to detect Bit Torrent communication.